Ensuring G Network Security Setup for IoT Devices
In the world of Internet of Things (IoT), where increasing numbers of devices are being connected to the internet, the risk of security breaches has also escalated. This raises concerns for network administrators and security experts. To address these concerns, the proper setup of a G Network Security for IoT devices is essential.
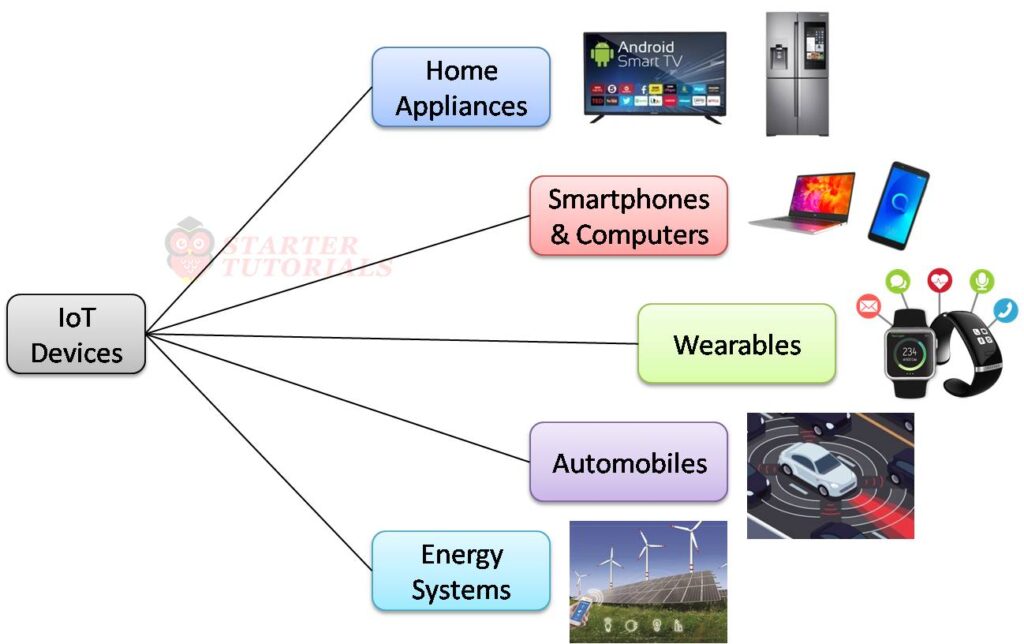
Understanding IoT Devices
IoT devices come in various forms, including smart speakers, thermostats, cameras, wearables, and appliances. While they bring added convenience to daily life, they also introduce unique cybersecurity risks. Each connected device can serve as a potential entry point for cybercriminals, compromising your network and sensitive data.
Key Considerations for IoT Device Security
To minimize the risks associated with IoT devices, the following key considerations should be taken into account:
- Device Security**: IoT devices should be designed with security in mind, utilizing robust security protocols to protect against attacks.
- Network Security**: IoT devices should be connected to a secure network that has robust security measures in place, including firewalls and intrusion detection systems.
- Application Security**: IoT applications and software should be updated regularly to patch vulnerabilities and prevent exploits.
Practical Measures for IoT Device Security
Based on GSMA's FS.60 IoT Security Guidelines, practical measures for IoT device security include:
- Secure Boot**: Ensuring that IoT devices start with a trusted boot process to prevent unauthorized modification.
- Firmware Signing**: Verifying firmware updates to prevent tampering and ensure authenticity.
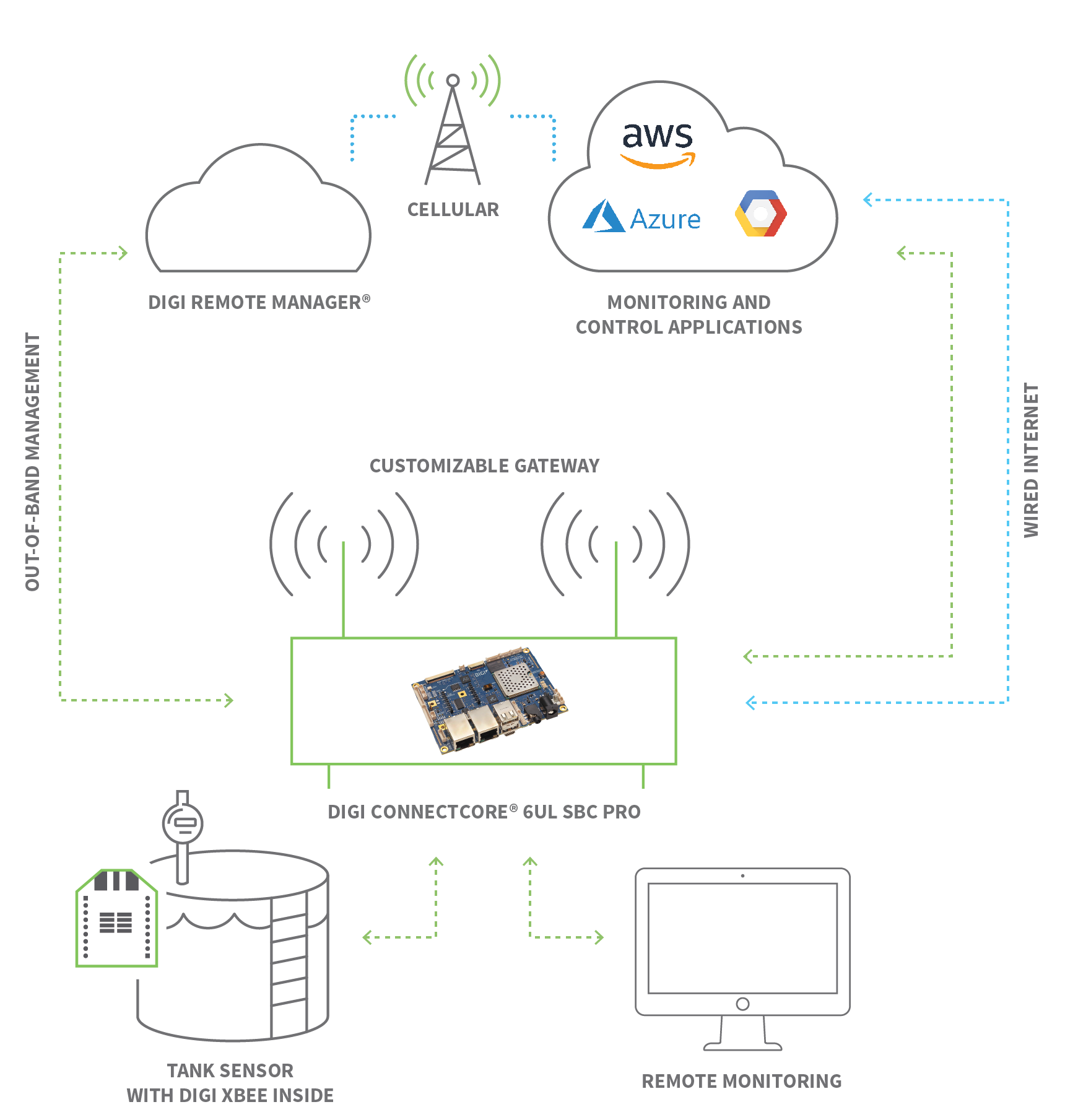
- End-to-End Encryption**: Encrypting data from the moment it's created to the moment it's received, ensuring confidentiality and integrity.
- Mutual Authentication**: Authenticating both the IoT device and the server it's connecting to, ensuring mutual trust and preventing impersonation attacks.
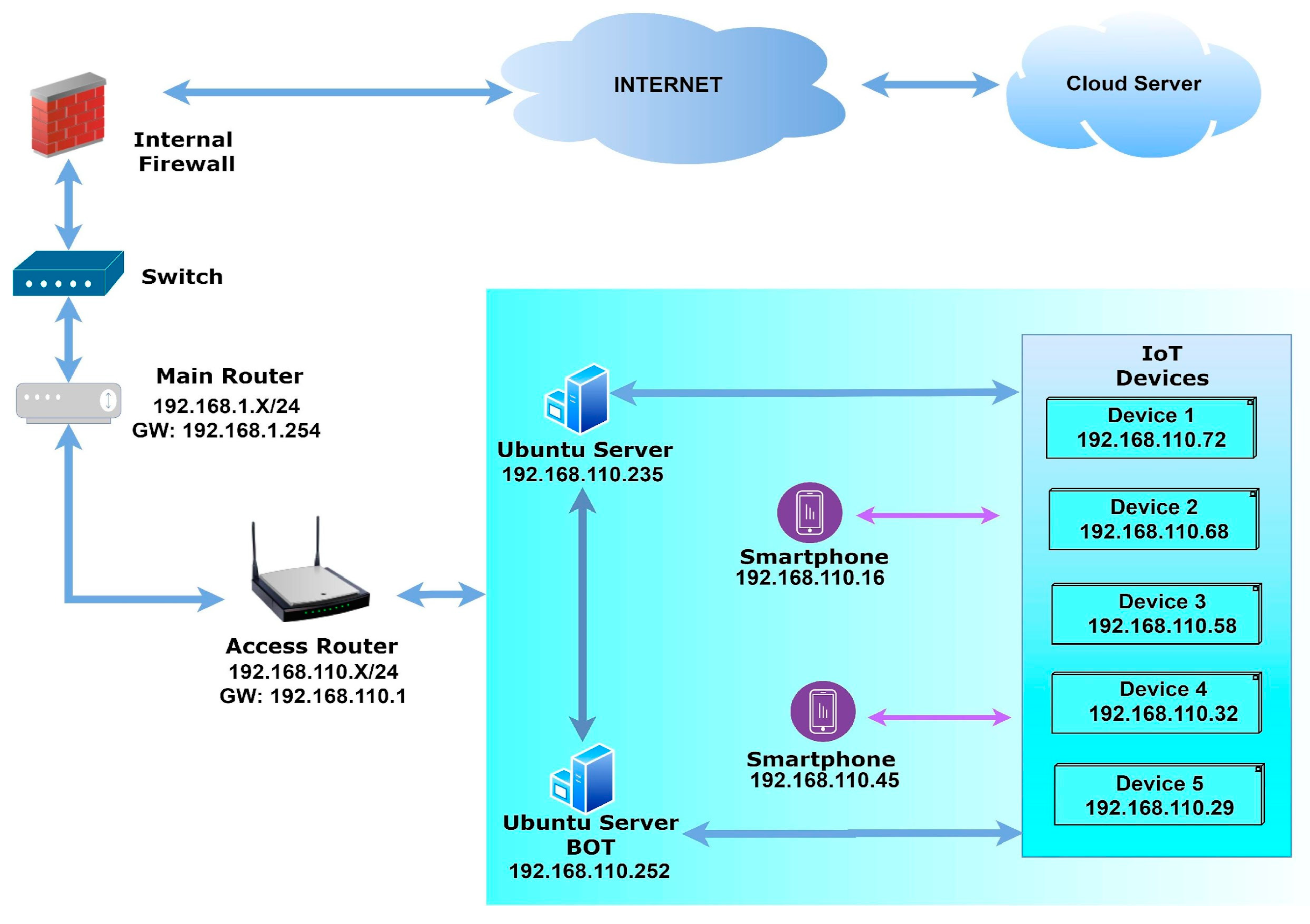
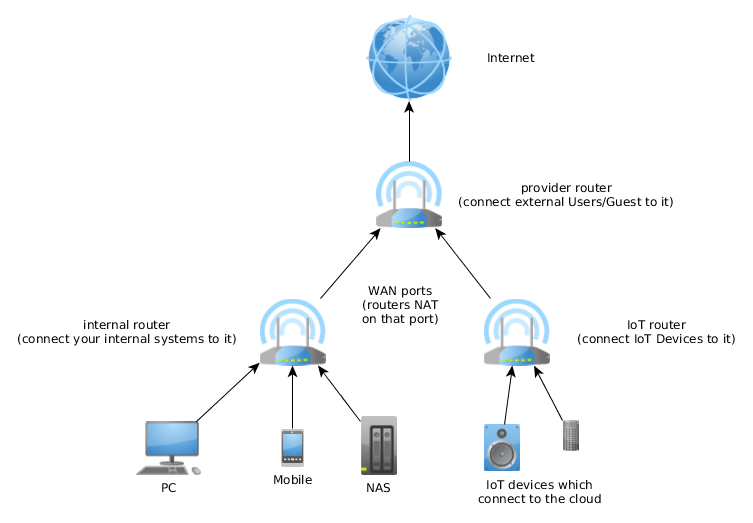
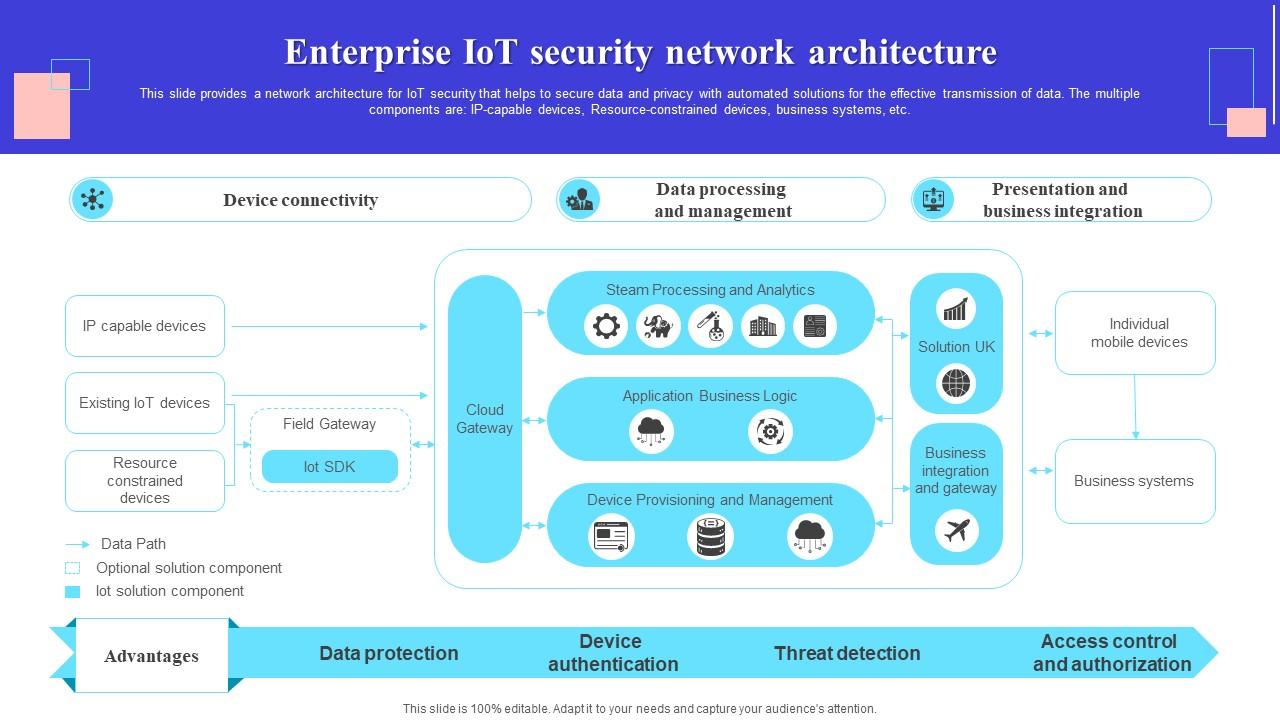
Network Setup for IoT Devices
When setting up a network for IoT devices, the following measures can be taken:
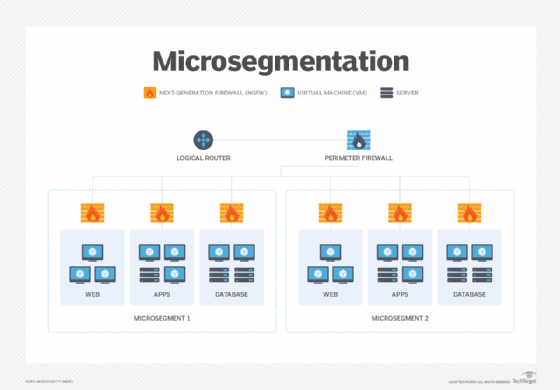
- Segmentation**: Isolate IoT devices from the rest of the network to prevent lateral movement in the event of a breach.
- Firewall Rules**: Configure firewalls to restrict access to IoT device management services to only the necessary IP address ranges.
- Guest Network**: Set up a guest network for IoT devices to prevent direct access to the main network.
Conclusion
Ensuring a secure network setup for IoT devices is crucial in today's interconnected world. By understanding the risks associated with IoT devices, implementing robust security measures, and following practical guidelines, network administrators can safeguard their networks against potential threats.
Final Thoughts
As the number of connected devices continues to grow, the importance of IoT device security cannot be overstated. By staying informed and taking proactive measures, network administrators can ensure the security of their networks and safeguard their users' sensitive data.