Ensuring the Security of Your G Wireless Network: Essential Measures to Protect Your Data
With the increasing reliance on wireless networks, the importance of G wireless network security measures cannot be overstated. The unfortunate reality is that an inadequately secured wireless network can serve as a gateway for malicious actors to compromise sensitive data and disrupt the entire network ecosystem.
Understanding the Importance of Wireless Network Security
Wireless network security is a multi-faceted approach designed to protect devices and networks connected in a wireless environment. In the absence of robust security measures, a networking device such as a wireless access point or a router can be accessed by anyone using a computer or mobile device within range of the router's wireless signal.
Effective G Wireless Network Security Measures
- Password Policies: Implementing a strict password policy is fundamental to securing your wireless network. This includes requirements for password strength, complexity, and length, as well as regular password updates.
- Encryption Standards: Utilize the latest encryption standards such as WPA2 and WPA3 to safeguard data transmission. Consider upgrading to WPA3 for advanced security features.
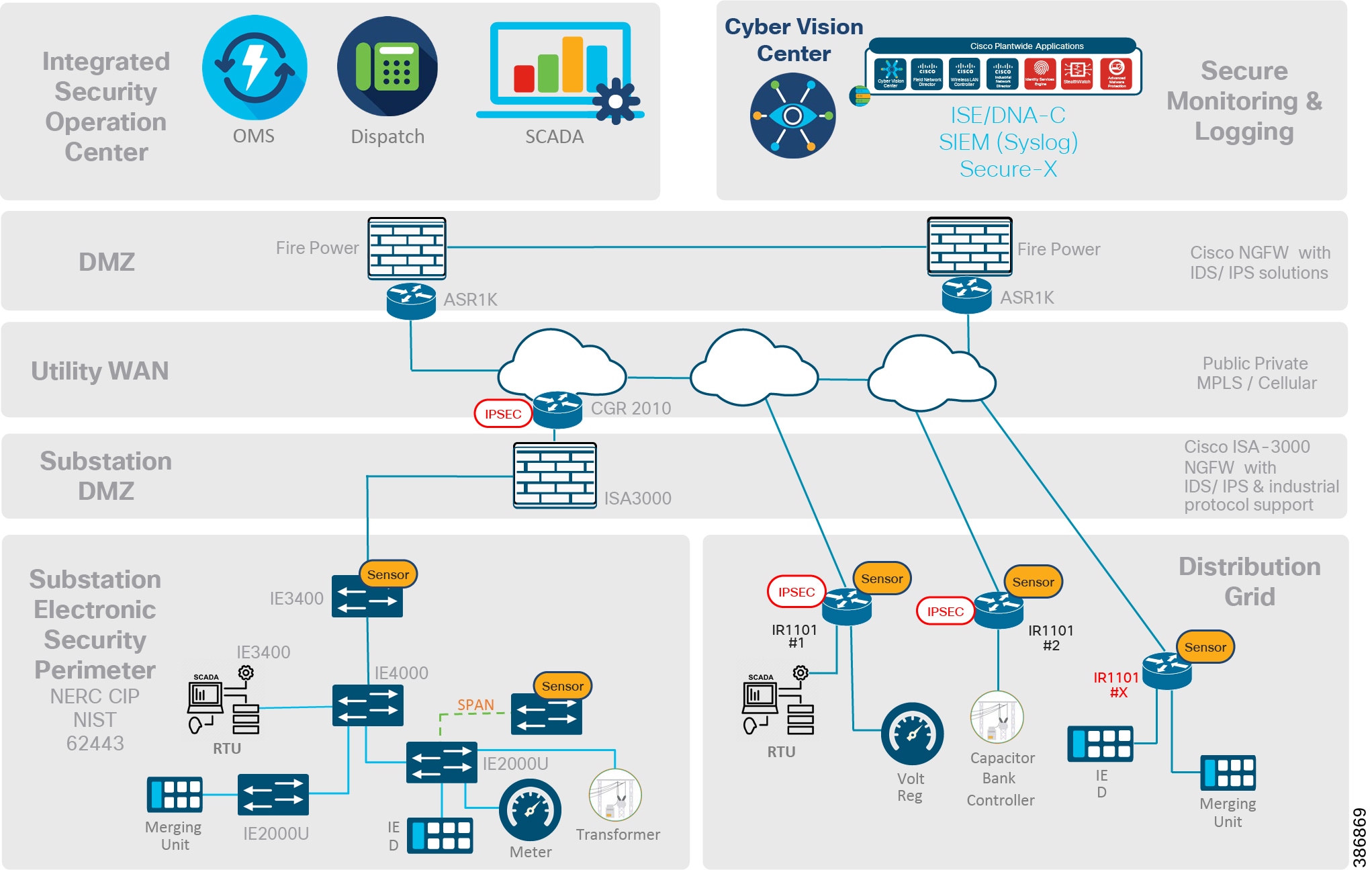
- Access Control List (ACL): Configure ACLs to regulate and filter incoming and outgoing network traffic based on IP addresses, protocols, and ports.
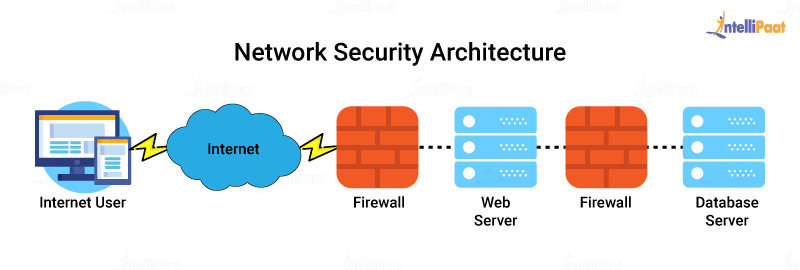
- Firewall Configuration: Implement a robust firewall configuration to block unauthorized access and malicious traffic from targeting your network.
- Network Segmentation: Segment your network to isolate sensitive areas, reducing the attack surface and hindering the spread of malware in the event of a breach.
- Regular Software Updates: Ensure your wireless network's firmware and software are regularly updated to prevent exploitation of known vulnerabilities.
- Virtual Private Network (VPN): Deploy a VPN solution for secure remote access and protect data transmitted over public networks.
- Network Monitoring: Engage in continuous network monitoring for anomalies and potential security threats.
- Employee Training: Educate employees and users about the importance of G wireless network security and best practices for securing devices and networks.
- Incident Response Plan: Establish a comprehensive incident response plan to address security breaches and minimize their impact.
- Security Audits: Regularly conduct security audits to identify vulnerabilities and ensure compliance with relevant security standards.
The Consequences of Neglecting G Wireless Network Security
/wireless-standards-802-11a-802-11b-g-n-and-802-11ac-816553-final-IL-5b50a1e3c9e77c003e1f7c00.png)
The consequences of neglecting G wireless network security measures can be severe, including but not limited to: unauthorized access to sensitive data, network downtime, financial losses due to data breaches or cyber attacks, compromised Intellectual Property, and reputational damage.
Conclusion
Protecting your G wireless network is a proactive measure that can safeguard your data, devices, and overall network ecosystem. By implementing a multi-layered approach of the outlined G wireless network security measures, you can ensure the integrity, confidentiality, and availability of your network, thereby promoting a secure and efficient digital environment.
Recommendations
- Enforce strict password policies and regular updates.
- Implement the latest WPA3 encryption standards for enhanced security.
- Configure Access Control Lists (ACLs) to control network traffic.
- Deploy a robust firewall configuration to block unauthorized access.
- Regularly update firmware and software to prevent exploitation of known vulnerabilities.
- Engage in continuous network monitoring for potential security threats.
- Provide employee training and awareness on G wireless network security.
- Develop and implement a comprehensive incident response plan.
- Regularly conduct security audits to ensure compliance and identify vulnerabilities.