Setting Up a Reliable G Wireless Network for Cloud-Based Security
In today's digital age, wireless networks have become an integral part of our daily lives. With the increasing demand for cloud-based services, securing your network has become more crucial than ever. In this article, we will discuss the importance of setting up a reliable G wireless network for cloud-based security and provide you with a comprehensive guide on how to do it.
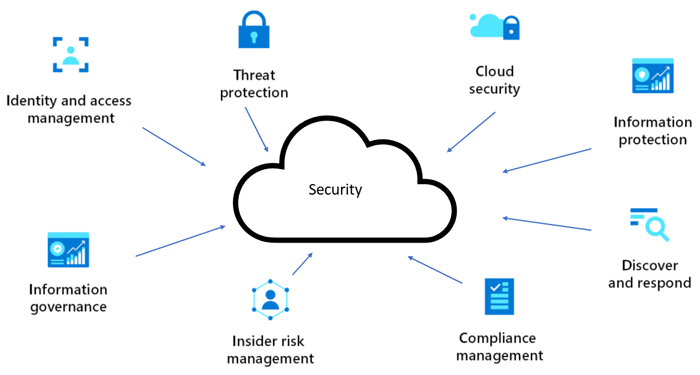
Why is Cloud-Based Security Important?
Cloud-based security is essential for several reasons. Firstly, it provides a secure and scalable infrastructure for businesses, allowing them to store and process data remotely. Secondly, cloud security solutions are easily accessible and can be managed from anywhere, using any device with an internet connection. This flexibility is particularly useful for employees working remotely, who require secure access to company resources.
5 Key Considerations for a Secure G Wireless Network
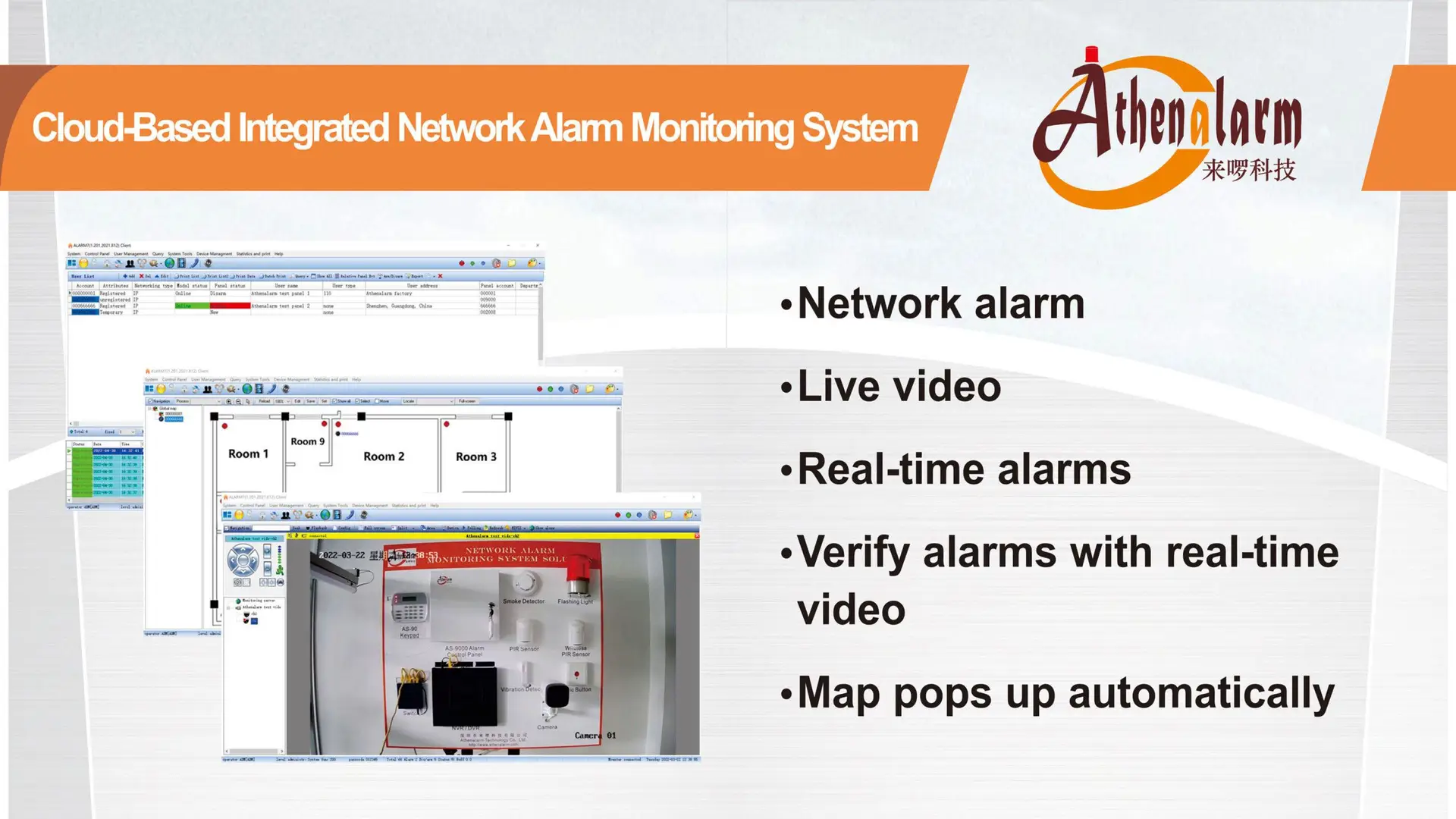
- Network Architecture: Ensure that your wireless network architecture is secure and scalable. Consider implementing a cloud-based network management system to monitor and control your network.
- Wireless Network Standard: Adopt the 802.11ac standard, which provides faster speeds and greater data transfer. Consider using a wireless router that supports this standard for optimal performance and security.
- Encryption: Implement WPA2 or WPA3 encryption, which provides advanced security features to protect your network from cyber threats. WPA2 provides strong encryption and is the recommended choice, but WPA3 is more secure and supports Opportunistic Wireless Encryption (OWE).
- Password Management: Ensure that you have secure password policies in place. Use a combination of letters, numbers, and special characters, and change passwords regularly to minimize the risk of a security breach.
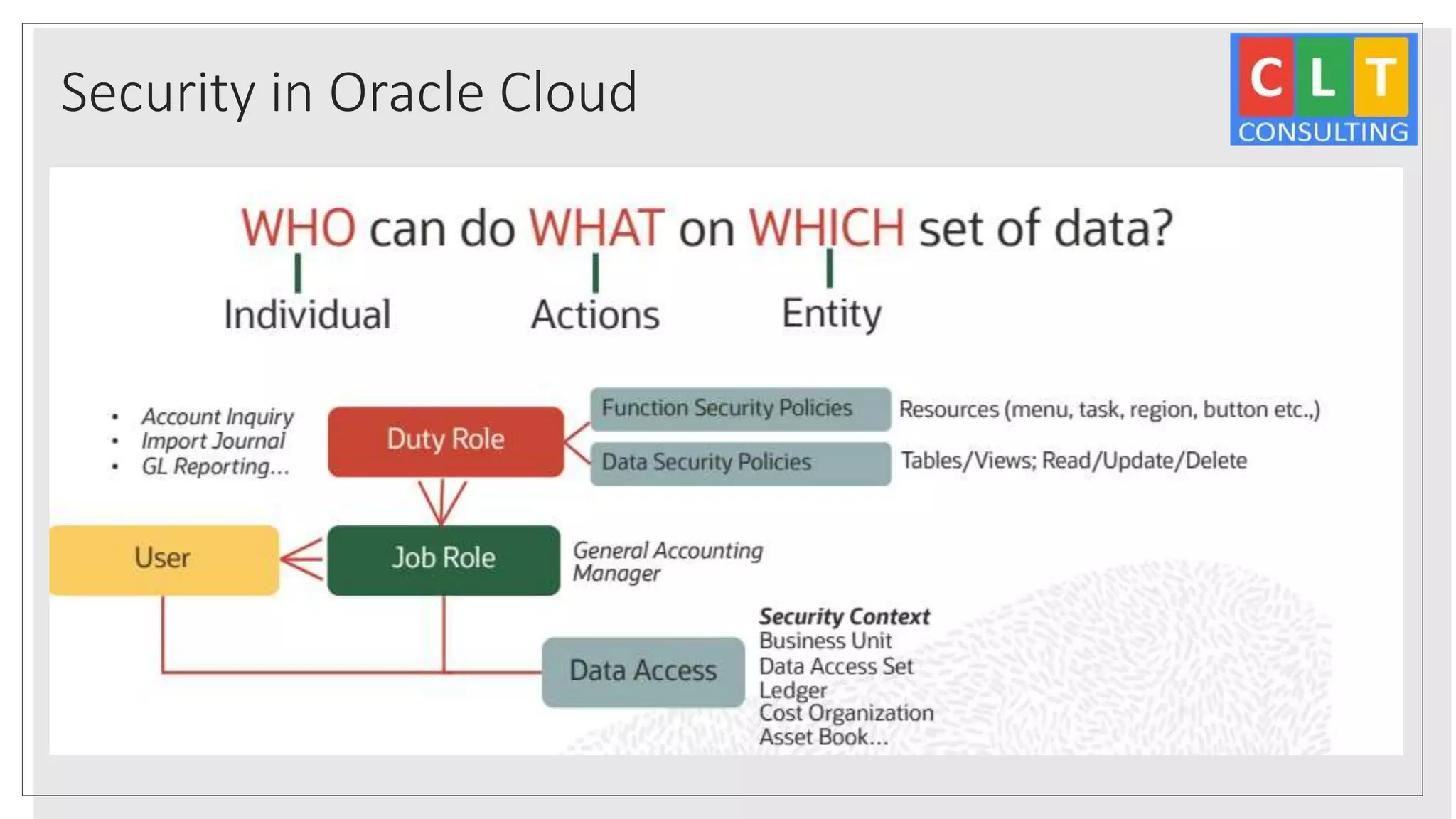
- Access Control: Implement access controls to limit who can access your network. Use a guest network for visitors and guest users, and implement guest access policies to limit their access to certain network resources.
Best Practices for Setting Up a Reliable G Wireless Network
Step 1: Plan Your Network
Plan your wireless network layout and ensure that it meets the needs of your business. Consider the size of your facility, the number of users, and the types of devices that will be used on the network.
Step 2: Choose Your Equipment

Choose a wireless router that supports the 802.11ac standard and WPA2 or WPA3 encryption. Consider the type and number of devices that will be connected to the network and select a router that can handle the traffic.
Step 3: Set Up Your Network
Set up your network by configuring the wireless router and components such as access points and switches. Ensure that all components are properly connected and configured.
Step 4: Secure Your Network
Implement WPA2 or WPA3 encryption and set up strong passwords and access controls. Configure guest access policies and limit the access of visitors and guest users to certain network resources.
Conclusion
Setting up a reliable G wireless network for cloud-based security requires careful planning, attention to detail, and a commitment to security. By following the best practices outlined in this article, you can establish a secure and scalable wireless network that meets the needs of your business.
Key Takeaways
- Cloud-based security is essential for businesses that require remote access to data and resources.
- A secure wireless network architecture is crucial for protecting against cyber threats.
- The 802.11ac standard is a good choice for wireless networks that require high-speed data transfer.
- Implement WPA2 or WPA3 encryption for strong password protection.
- Use a guest network for visitors and guest users to minimize the risk of a security breach.