Designing the Future of Airports: A Comprehensive Guide to G Wireless Network Configuration
As airports continue to evolve and become smarter, high-reliable connectivity is no longer just a luxury – it's a necessity. With the increasing demand for online services and mobile connectivity, airports face unprecedented challenges in providing seamless, secure, and robust wireless network infrastructure. In this article, we will delve into the key considerations for designing a G wireless network configuration for airports, focusing on scalability, security, and passenger experience.
Understanding the Need for G Wireless Network Configuration
- With the growing dependency on digital services, airports face the challenges of providing reliable, secure, and high-speed connectivity to passengers, staff, and IoT devices.
- Wireless connectivity is no longer just a convenience – it's a fundamental requirement for passenger experience, operational efficiency, and safety.
- A reliable G wireless network configuration can significantly enhance the passenger experience, streamline airport operations, and increase revenue-generating opportunities.
Designing a Scalable G Wireless Network for Airports
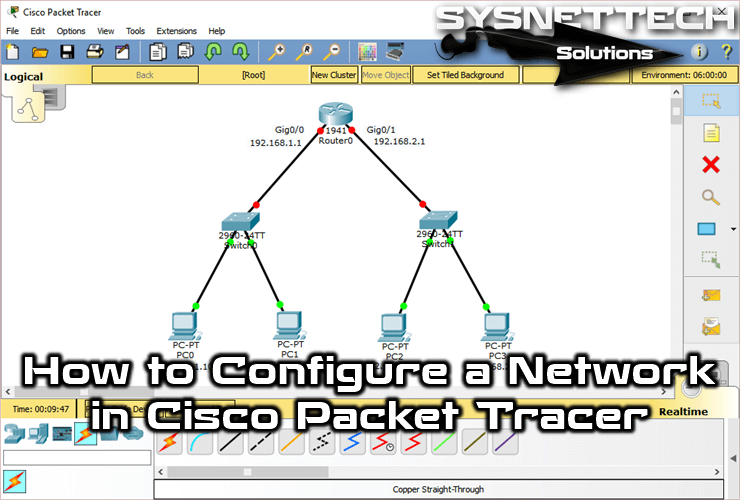
Designing a G wireless network configuration for airports involves careful consideration of scalability, security, and network architecture. Here are some key design principles to consider:
- Modular Architecture: Adopt a modular architecture that allows for easy upgrades, maintenance, and scalability.
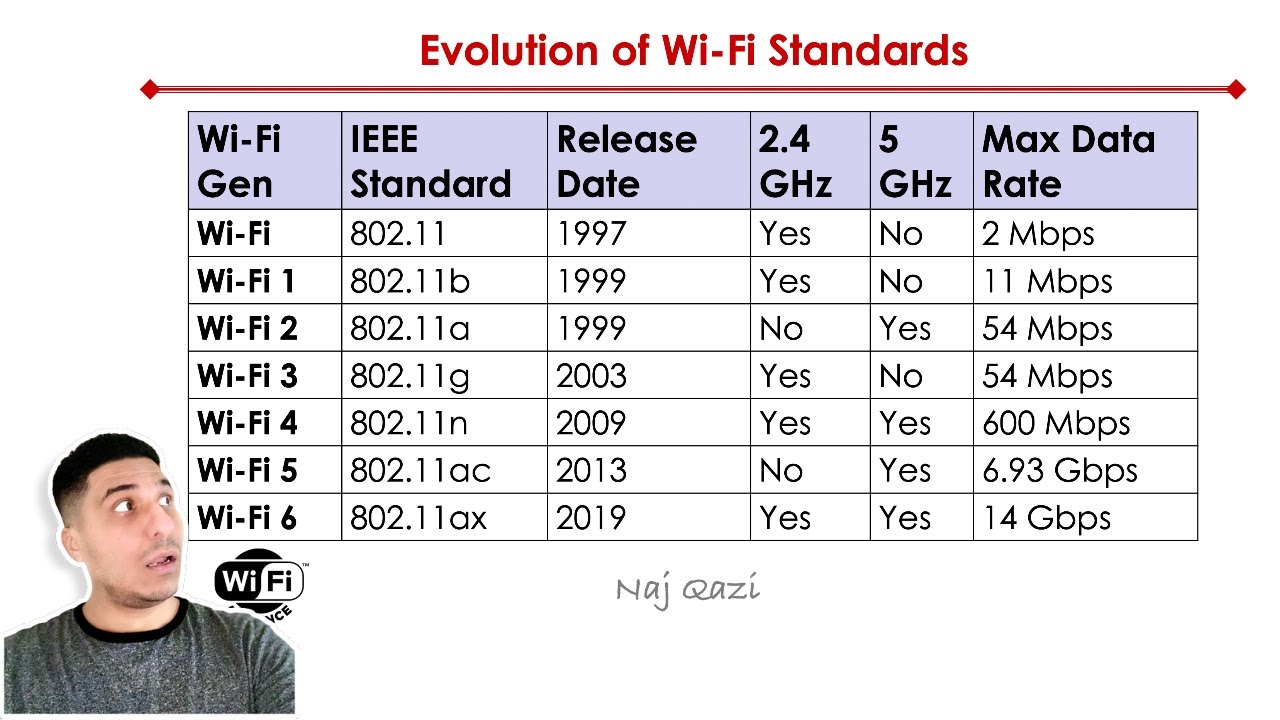
- Wireless Solution: Implement a wireless solution that supports a range of devices, including IoT devices, laptops, smartphones, and tablets.
- Network Segmentation: Implement network segmentation to ensure secure, isolated communication between different airport systems and networks.
- Redundancy: Implement redundancy to ensure continued network availability in case of equipment failures or network overhead.
Security Considerations for G Wireless Network Configuration
Sovereign and availability are critical considerations when it comes to wireless tuning for airports. Here are some security considerations to keep in mind:
- Authentication: Implement strong authentication processes, including WPA2 or WPA3, to ensure secure access to the wireless network.
- Encryption: Implement industry-standard encryption protocols, including AES, to protect data in transit.
- Access Control: Implement access control mechanisms to restrict access to specific levels of the network and prevent unauthorized access.
- Network Segmentation: Implement network segmentation to prevent lateral movement in the event of a breach.

Case Study: Implementing G Wireless Network Configuration at a Modern Airport
A recent case study on the implementation of G software-defined access (SDA) design guidelines at a leading airport demonstrates the benefits of a well-planned and executed G wireless network configuration:
- The airport implemented a modular, scalable SDA design that enabled seamless connectivity, efficient network administration, and stepped-up service capabilities.
- The solution provided high-performance, scalable, and secure access to critical applications, appliances, and end devices, including Wi-Fi-enabled boards and keyboards.
- The implementation resulted in improved capacity, faster speeds, and higher performance, along with roaming and connectivity throughout the airfield.
Conclusion
In conclusion, designing a G wireless network configuration for airports requires careful consideration of scalability, security, and network architecture. By implementing a modular, secure, and redundant network design, airports can ensure reliable and high-speed connectivity, enhance the passenger experience, streamline airport operations, and increase revenue-generating opportunities. With a well-planned G wireless network configuration, airports can evolve into smart infrastructures that offer seamless connectivity, enhanced efficiency, and improved passenger experiences.
Recommendations
Our top recommendations for designing a G wireless network configuration for airports include:
- Implementing a modular, scalable network architecture that supports high-performance, high-speed connectivity.
- Implementing strong security measures, including authentication, encryption, and access control.
- Network segmentation to prevent lateral movement in the event of a breach.
- Regular network monitoring and maintenance to ensure continued network availability and reliability.